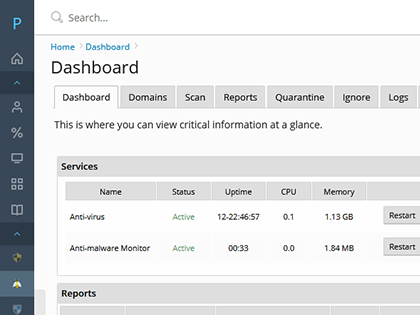
Sentinel Anti-malware
Linux Malware Detect
Anti-malware engine designed around the threats faced in todays hosting environments. It uses multifaceted threat data from network edge IPS, community data, ClamAV, and user submission systems to extract malware that is actively being used in attacks.
ClamAV Anti-virus
The ClamAV® open source multi-threaded scanner daemon detects trojans, viruses, malware and other malicious threats. Extended signatures from Malware Expert provide ultimate detection of PHP based malware.
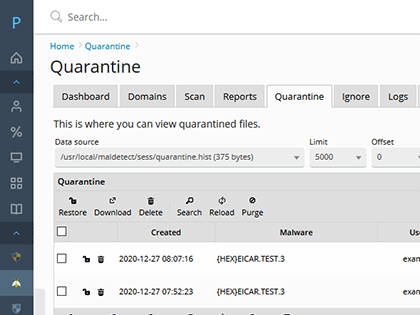
Quarantine Malware
Malware can be quatantined storing threats in a safe fashion with no permissions. You can optionally restore files to original path, owner and permissions.
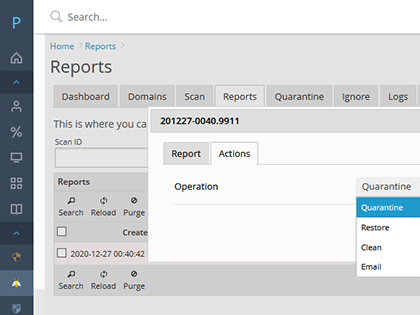
Clean Infected Files
Cleaner rules will attempt to remove malware injected strings. Supports base64 and gzinflate (base64 injected malware). After clean is performed it will be re-scanned and verify that the clean was successful.
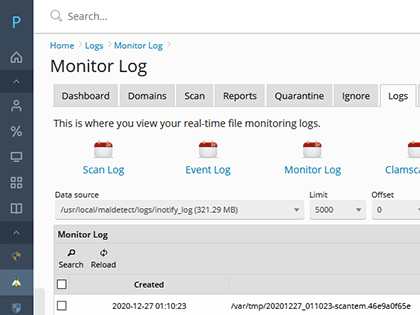
Real-time Scanning
Kernel based inotify real time file scanning of created/modified/moved files. Monitor your entire vhosts directory tree an instantly scan any changed files. All of its resources are inside kernel memory and has a very small cpu usage and userspace footprint in memory.
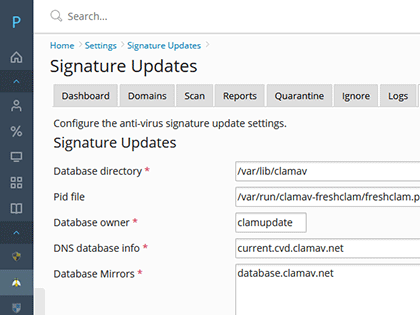
Signature updates
Signatures are updated typically once per day or more frequently depending on incoming threat data, IPS malware extraction and other sources. Signatures are derived from tracking active in the wild threats that are currently circulating. Threat data includes Network Edge IPS, community, ClamAV, and user submissions.
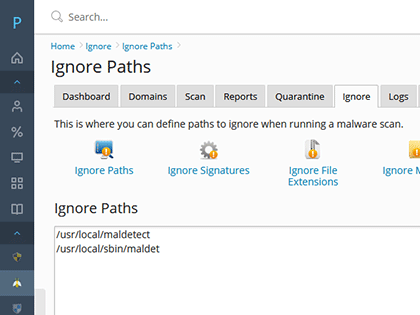
Ignore Options
Sentinel gives you multiple options to minimize any false positives. Ignore specific paths, file extensions or whitelist bad signatures with just a few clicks.
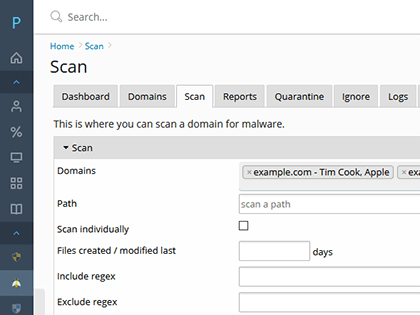
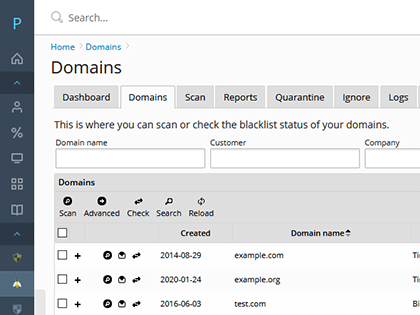
On-demand Scanning
Sentinel allow you scan a domains web folder with just a few clicks. The scan can automatically quarantine detected threats (if enabled) or allow you to quarantine, clean malware or email a report the the customer.