Warden Protection
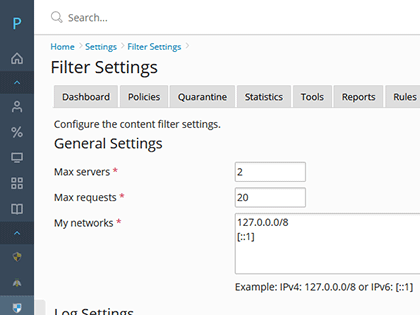
Amavis Content Filter
Amavis is a high-performance interface between Postfix, SpamAssassin, and ClamAV. Amavis has been the gold standard used by large email providers for over a decade.
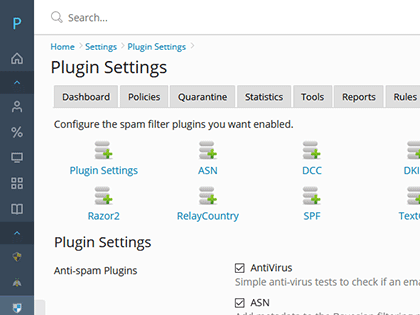
SpamAssassin Anti-spam
Warden super charges SpamAssassin by providing deep integration with Plesk and enabling all of the most effective SpamAssassin plugins.
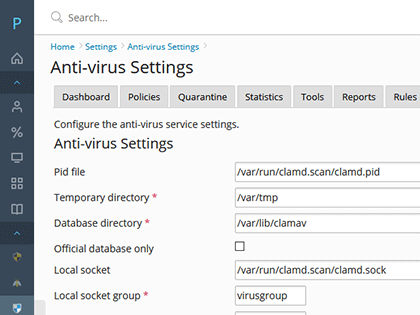
ClamAV Anti-virus
The ClamAV open source multi-threaded scanner daemon detects trojans, viruses, malware and other malicious threats. Extended signatures provide protection against Phishing, Scam, Casino, porn and other general spam.
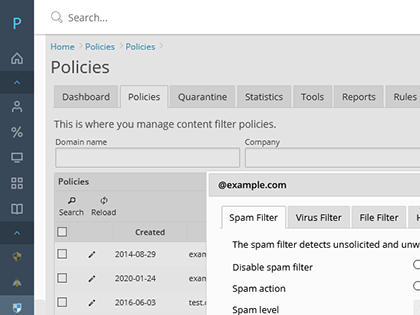
Hierarchical Policies
Policies are hierarchical meaning that you can set server wide, domain, and mailbox level filter policies. All child policies will inherit from the parent unless they are overwritten at the child level.
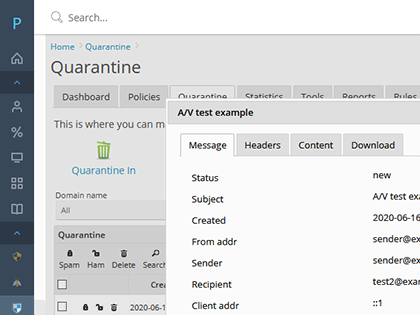
Quarantine Support
Quarantine spam, viruses, banned attachments, and mail with non-compliant email headers. Customers can login to manage their quarantined messages. False positives can easily be trained and released back to the original recipients mailbox.
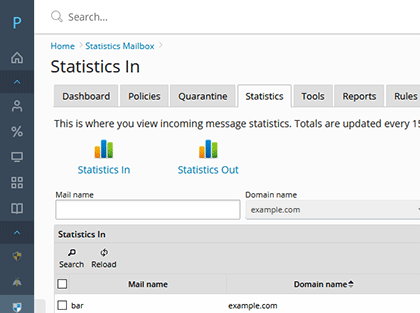
Statistics and Reporting
An anti-spam and anti-virus system is only as good as its reporting. We have written 50 of the most detailed spam, ham, and virus reports anywhere.
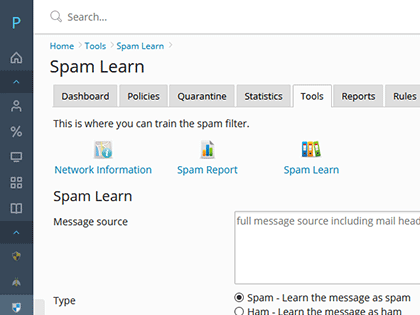
Learning and Reputation
Tracks scores from previously received messages and adjust the message score, either by boosting messages from senders who send ham or penalizing senders who have sent spam previously.
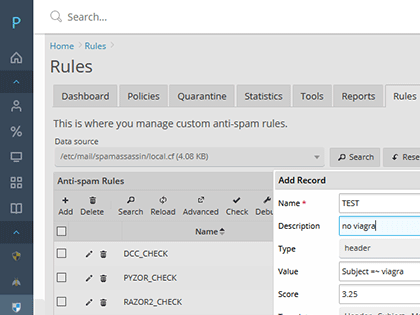
Custom Rule Builder
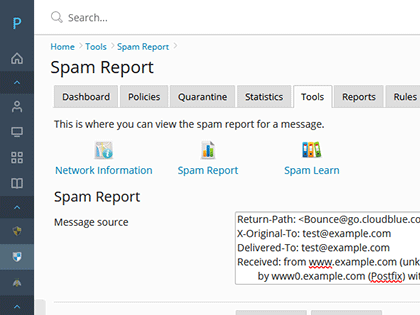
Add custom SpamAssassin rules right though the Warden interface. Apply rules matching the message header, subject, body or even specific URIs.
Network Based Tests
Full support for Razor 2, Pyzor, and DCC network based tests. These network based tests can dramatically improve detecting bulk email and spam.
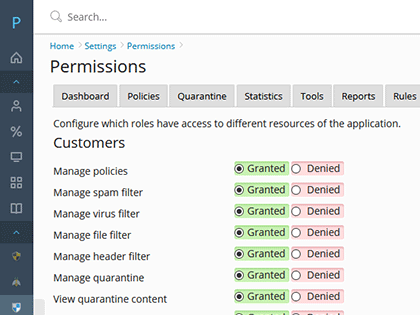
Multi-Role Access
Warden fully supports giving resellers, customers, and mail users access to different parts of the Warden application. Enable your customers to help themselves without resorting to costly support calls.
IMAP/POP3 Tracking
Track who is logged into the dovecot service. This makes it easy to see if a customer can access their mailbox.
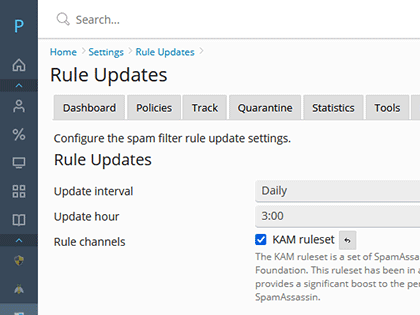
Third Party Rule Support
Boost the performance and efficacy of a stock installation of Amavis using third party rulesets.
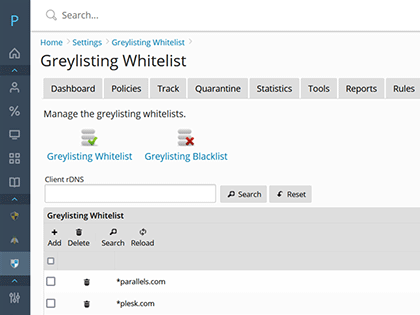
Greylisting
Greylisting will tell the mail server to temporarily reject any email from a sender it does not recognize. If the mail is legitimate, the originating server will try again after a delay, and if sufficient time has elapsed, the email will be accepted.
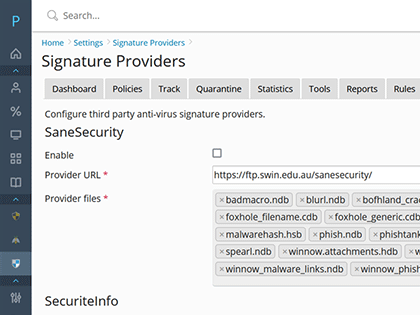
Extended Signatures
Extend ClamAV using free third-party signature databases provided by Sanesecurity, Securiteinfo, and URLhaus. This can dramatically increase ClamAVs detection rates without costing you anything.
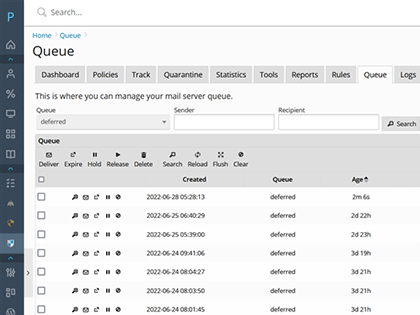
Queue Management
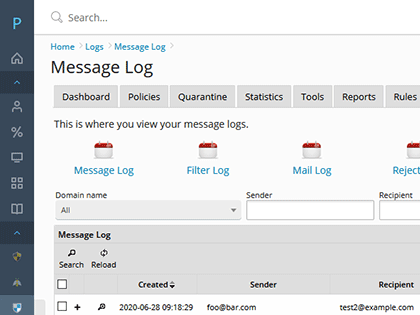
The queue management area gives admins the tools they need to identify compromised email accounts or PHP forms that are being abused on the server.
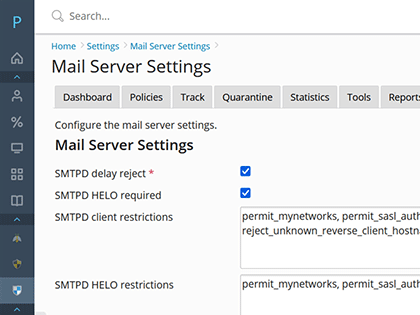
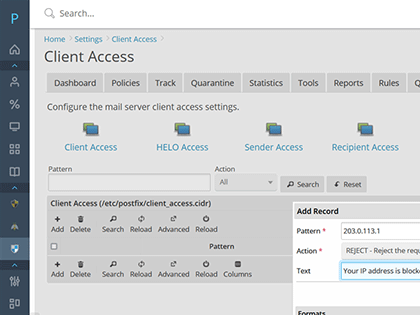
Restriction Management
Manage SMTPD restrictions directly though the Warden interface. Harden Postfix so that the bulk of spam get rejected at the SMTPD level efficiently before it gets processed by Amavis helping to reduce server load.
Mail Server Access Management
Admins have the ability to whitelist or blacklist at the SMTPD level by client IP address, CIDR, HELO/EHLO hostname, envelope sender, and envelope recipient.